FRACTION MAGIC – PART 1: VOTES ARE BEING COUNTED AS FRACTIONS INSTEAD OF AS WHOLE NUMBERS

1 – SUMMARY –
This report summarizes the results of our review of the GEMS election management system, which counts approximately 25 percent of all votes in the United States. The results of this study demonstrate that a fractional vote feature is embedded in each GEMS application which can be used to invisibly, yet radically, alter election outcomes by pre-setting desired vote percentages to redistribute votes. This tampering is not visible to election observers, even if they are standing in the room and watching the computer. Use of the decimalized vote feature is unlikely to be detected by auditing or canvass procedures, and can be applied across large jurisdictions in less than 60 seconds.
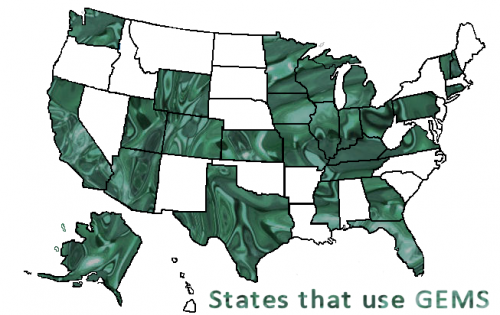 GEMS vote-counting systems are and have been operated under five trade names: Global Election Systems, Diebold Election Systems, Premier Election Systems, Dominion Voting Systems, and Election Systems & Software, in addition to a number of private regional subcontractors. At the time of this writing, this system is used statewide in Alaska, Connecticut, Georgia, Mississippi, New Hampshire, Utah and Vermont, and for counties in Arizona, California, Colorado, Florida, Illinois, Indiana, Iowa, Kansas, Kentucky, Massachusetts, Michigan, Missouri, Ohio, Pennsylvania, Tennessee, Texas, Virginia, Washington, Wisconsin and Wyoming. It is also used in Canada.
GEMS vote-counting systems are and have been operated under five trade names: Global Election Systems, Diebold Election Systems, Premier Election Systems, Dominion Voting Systems, and Election Systems & Software, in addition to a number of private regional subcontractors. At the time of this writing, this system is used statewide in Alaska, Connecticut, Georgia, Mississippi, New Hampshire, Utah and Vermont, and for counties in Arizona, California, Colorado, Florida, Illinois, Indiana, Iowa, Kansas, Kentucky, Massachusetts, Michigan, Missouri, Ohio, Pennsylvania, Tennessee, Texas, Virginia, Washington, Wisconsin and Wyoming. It is also used in Canada.
Fractionalized vote:
Instead of “1” the vote is allowed to be 1/2, or 1+7/8, or any other value that is not a whole number.
What fractionalized votes can do:
They allow “weighting” of races. Weighting a race removes the principle of “one person-one vote” to allow some votes to be counted as less than one or more than one. Regardless of what the real votes are, candidates can receive a set percentage of votes. Results can be controlled. For example, Candidate A can be assigned 44% of the votes, Candidate B 51%, and Candidate C the rest.
GEMS fractionalizes votes in three places:
- The “Summary” vote tally, which provides overall election totals for each race on Election Night
- The “Statement of Votes Cast”, which provides detailed results by precinct and voting method (ie. Polling, absentee, early, provisional)
- The “undervote” count
Fractions in results reports are not visible.Votes containing decimals are reported as whole numbers unless specifically instructed to reveal decimals (which is not the default setting). All evidence that fractional values ever existed can be removed instantly even from the underlying database using a setting in the GEMS data tables, in which case even instructing GEMS to show the decimals will fail to reveal they were used.
Source code: Instructions to treat votes as decimal values instead of whole numbers are inserted multiple times in the GEMS source code itself; thus, this feature cannot have been created by accident.
Fractionalizing the votes which create the Summary Results allows alteration of Election Night Web results and results sent to the Secretary of State, as well as results available at and local election officials.
Fractionalizing the “Statement of Votes Cast” allows an extraordinary amount of precision, enabling alteration of results by specific voting machine, absentee batch, or precinct. Vote results can be altered for polling places in predominantly Black neighborhoods, and can parse out precincts within a mixed batch of early or absentee votes.
Fractionalizing the undervote category allows reallocation of valid votes into undervotes.
Voting rights abomination
According to programmer notes, a weighted race feature was designed which not only gives some votes more weight than others, but does so based on the voter’s identity. Ballots are connected to voters, weights are assigned to each voter per race, stored in an external table not visible in GEMS. Our testing shows that one vote can be counted 25 times, another only one one-thousandth of a time, effectively converting some votes to zero.
The study was prompted by two issues: (1) Anomalies in elections in Shelby County, Tennessee, which uses the GEMS election management system, in which inconsistencies were observed in reporting of results by GEMS; and (2) Concerns raised regarding the presence of middlemen during the election process, such that a single individual gains remote access to the election management program, in some cases in multiple jurisdictions.
The questions we examine are these:
Can election outcomes be controlled with enough versatility to allow a national impact? Does any mechanism exist that would enable a political consultant or technician to capture elections for repeat customers?
If the necessary features exist within the election management system to facilitate this:
Were such features embedded accidentally or on purpose; for what stated purpose were such features installed; if a reason was given, is that reason justifiable?
How might risks associated with inside access be mitigated?
Next:
Part 2: Context, Background, Deeper, Worse http://blackboxvoting.org/fraction-magic-2
All:
Part 1: Votes are being counted as fractions instead of as whole numbers http://blackboxvoting.org/fraction-magic-1
Part 2: Context, Background, Deeper, Worse http://blackboxvoting.org/fraction-magic-2
Part 3: Proof of code http://blackboxvoting.org/fraction-magic-3
Part 4: Presidential race in an entire state switched in four seconds http://blackboxvoting.org/fraction-magic-4
Part 5: Masters of the Universe http://blackboxvoting.org/fraction-magic-5
Part 6: Execution capacity – coming – http://blackboxvoting.org/fraction-magic-6
Part 7: Solutions and Mitigations – coming – http://blackboxvoting.org/fraction-magic-7
Part 2: Context, Background, Deeper, Worse http://blackboxvoting.org/fraction-magic-2
Part 3: Proof of code http://blackboxvoting.org/fraction-magic-3
Part 4: Presidential race in an entire state switched in four seconds http://blackboxvoting.org/fraction-magic-4
Part 5: Masters of the Universe http://blackboxvoting.org/fraction-magic-5
Part 6: Execution capacity – coming – http://blackboxvoting.org/fraction-magic-6
Part 7: Solutions and Mitigations – coming – http://blackboxvoting.org/fraction-magic-7
* * * * *
 Bennie Smith is a Memphis-based application developer for an electrical manufacturing company. He is also a political strategist who has developed a micro-targeting application that predicts voter turnout. In August 2014 he was approached by a number of candidates who insisted that their elections had been stolen. He disagreed with the group and offered to look into how the system works. After discovering a number of irregularities, Smith began to research how votes that originate from the same source can change once they get into the GEMS vote tabulation program. Smith’s attention to these anomalies uncovered an extraordinarily high-risk tampering mechanism and ultimately provided a new infrastructure for analyzing questionable election results.
Bennie Smith is a Memphis-based application developer for an electrical manufacturing company. He is also a political strategist who has developed a micro-targeting application that predicts voter turnout. In August 2014 he was approached by a number of candidates who insisted that their elections had been stolen. He disagreed with the group and offered to look into how the system works. After discovering a number of irregularities, Smith began to research how votes that originate from the same source can change once they get into the GEMS vote tabulation program. Smith’s attention to these anomalies uncovered an extraordinarily high-risk tampering mechanism and ultimately provided a new infrastructure for analyzing questionable election results.